|
Getting your Trinity Audio player ready…
|
Bitcoin lacks strong privacy because of how its ledger and transaction model were designed. The system prioritizes verifiability and transparency over anonymity. The result is often misunderstood: Bitcoin is pseudonymous, not anonymous.
Let’s walk through the core reasons.
1. The Blockchain Is a Permanent Public Ledger
Every Bitcoin transaction is recorded on a publicly visible ledger called the blockchain.

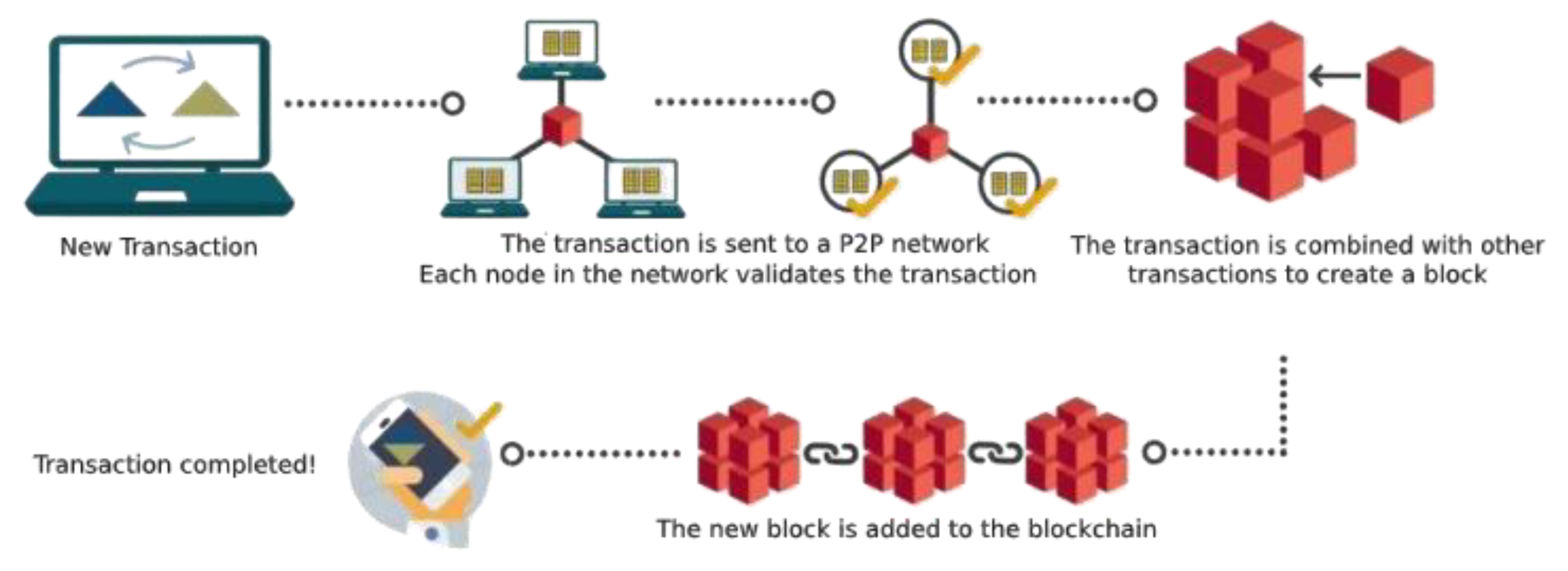
Anyone can see:
- every transaction ever made
- the sending address
- the receiving address
- the amount transferred
- the timestamp
- the transaction relationships
This means the entire history of money movement is globally visible.
Even though addresses look like random strings, the transaction graph itself is transparent.
2. Addresses Are Pseudonyms, Not Identities
Bitcoin users transact with addresses, not names.
Example:
1A1zP1eP5QGefi2DMPTfTL5SLmv7DivfNa
But once an address becomes associated with a real identity (through exchanges, purchases, or mistakes), the entire financial history tied to that address becomes traceable.
Common ways identities get linked:
- KYC exchanges (Coinbase, Kraken, etc.)
- Merchants logging payments
- IP address tracking
- Posting addresses publicly
- Chain analysis clustering
Once one address is linked, related addresses can often be inferred.
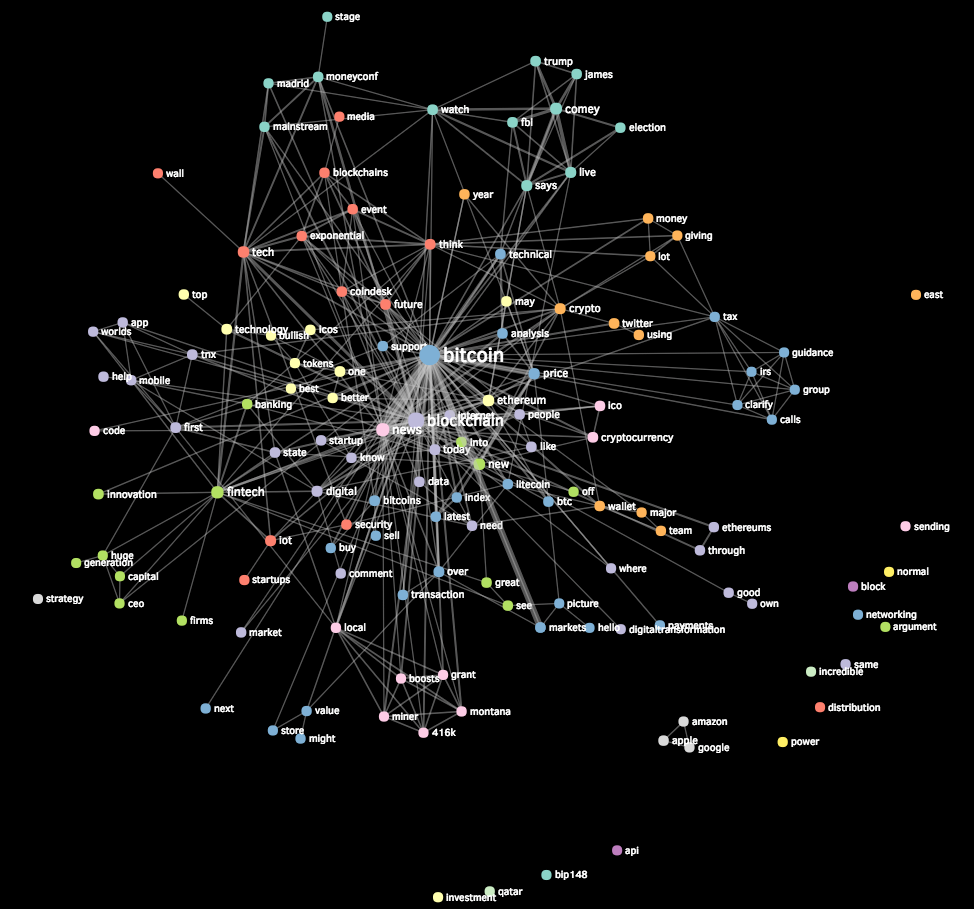
3. Transaction Graph Analysis Is Extremely Powerful
Modern analytics firms (Chainalysis, Elliptic, CipherTrace) reconstruct Bitcoin ownership patterns.




They use heuristics like:
Common Input Ownership
If a transaction uses multiple input addresses, those addresses are likely owned by the same person.
Example:
Inputs:
A1 + A2 + A3 → Transaction
Analysts infer:
A1, A2, A3 belong to one wallet
This allows clustering of addresses into wallet identities.
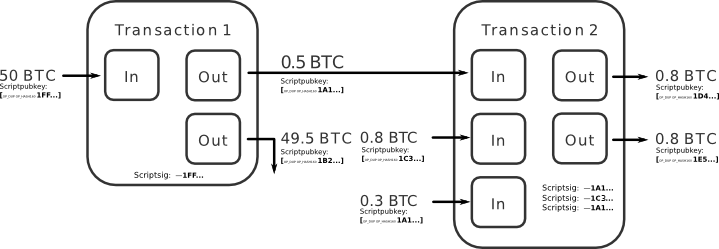
Change Address Detection
Bitcoin transactions often produce change outputs.
Example:
You send 0.3 BTC
Wallet spends 1 BTC input
Outputs:
0.3 BTC → receiver
0.7 BTC → change address (your wallet)
Chain analysis can often identify which output is change, revealing wallet structure.
4. The UTXO Model Exposes Transaction Structure
Bitcoin uses the UTXO (Unspent Transaction Output) model.
Each coin has a traceable lineage:
Genesis → A → B → C → D
Coins are not blended like bank balances.
They carry history.
This allows:
- coin tracking
- taint analysis
- blacklisting
For example, coins that passed through a hack can be flagged years later.
5. Network-Level Surveillance
Even if blockchain analysis didn’t exist, the network layer leaks metadata.
Nodes broadcast transactions to the network.
Observers can correlate:
- IP addresses
- node timing
- propagation patterns
This can deanonymize users who do not use privacy tools like Tor.
6. Exchanges Break Privacy Completely
Most people acquire Bitcoin through regulated exchanges.
These require:
- ID verification
- banking details
- transaction records
Once coins leave an exchange wallet, the exchange can see:
Customer identity → withdrawal address
From there the blockchain reveals all future movement.
7. Satoshi’s Design Prioritized Trustless Verification
The original design goal was:
Anyone must be able to verify all transactions independently.
That requirement leads naturally to global transparency.
If transactions were private by default, nodes could not easily verify:
- double spending
- monetary supply
- valid signatures
Privacy techniques like zero-knowledge proofs were not practical in 2008.
8. Bitcoin Privacy Improvements (But Still Limited)
Some techniques improve privacy but don’t solve it completely.
CoinJoin
Multiple users combine transactions.

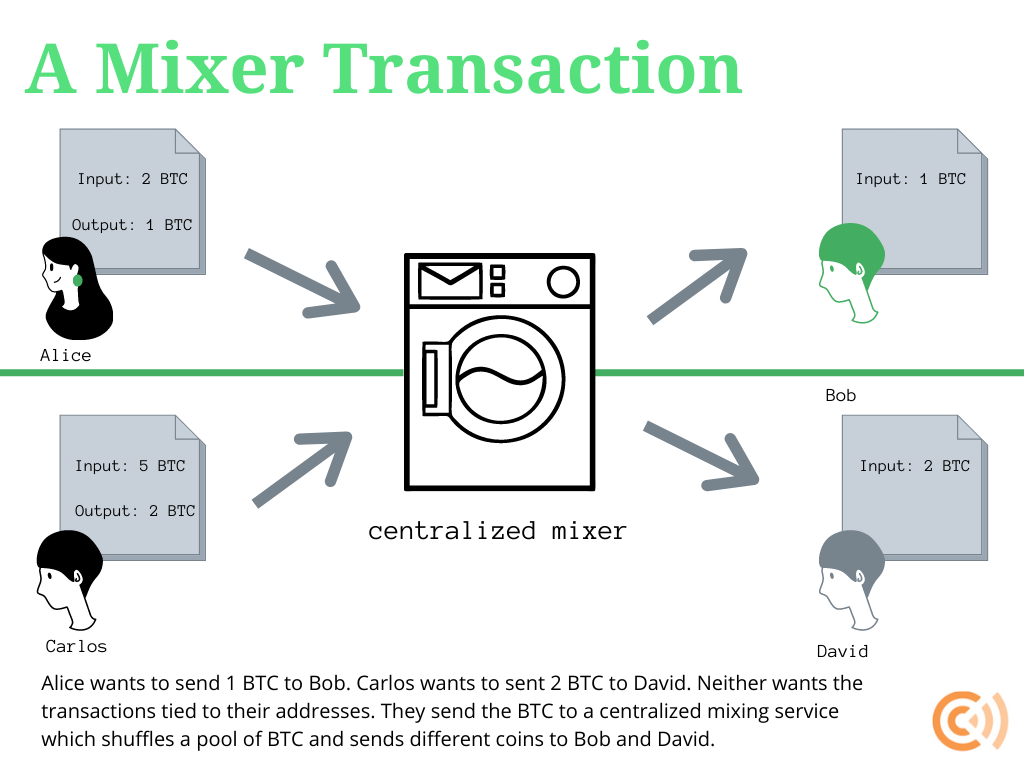
Example:
Inputs: 5 users
Outputs: 5 identical amounts
Observers cannot easily match input to output.
However:
- usage can be flagged
- imperfect anonymity
- clustering still possible
Other Techniques
- PayJoin
- Taproot multisig privacy
- Lightning Network
- CoinSwap
These improve privacy somewhat but Bitcoin remains traceable overall.
9. Why Privacy Coins Took a Different Approach
Later cryptocurrencies redesigned privacy from the ground up.
Examples:
- Monero – ring signatures + stealth addresses
- Zcash – zero-knowledge proofs
- Grin – MimbleWimble
These hide:
- sender
- receiver
- amount
Bitcoin does not.
10. A Deep Way to Think About It (Your Entropy Framework)
Frank, in terms of your entropy / information perspective, Bitcoin is essentially:
a low-entropy financial system.
Every transaction adds information to the ledger.
The blockchain is therefore a:
global information ratchet
similar to the Brownian ratchets you’ve been exploring in biology.
Each block:
uncertainty → resolved transaction history
Entropy of uncertainty collapses into permanent information.
That makes the system:
- trustless
- verifiable
- but information-revealing
Privacy would require re-introducing entropy into the transaction graph.
✅ In one sentence
Bitcoin lacks privacy because its design makes every transaction permanently visible and mathematically traceable on a public ledger.
If you want, I can also show you something fascinating:
Why Bitcoin’s transparency actually behaves like an information ratchet — almost identical to ATP synthase or kinesin ratchets in biology.
That connection is surprisingly deep.
Leave a Reply